Physical security is becoming increasingly complex, yet many teams still rely on outdated tools to manage it. While IT has embraced digital asset management, physical security is stuck with static PDFs, aging CAD files, and spreadsheets that are obsolete the moment they’re printed.
Effective asset visibility requires a total data picture that includes the physical location of hardware, its operational health, and proactive insights into potential failure points.
When devices fail, the lack of a living record forces teams to waste hours searching through physical ceilings and obsolete files. This information gap leaves critical questions unanswered: the device’s identity, its service history, and its warranty status.
Security teams gain greater operational resilience by transforming static documentation into real-time, actionable system intelligence and grounding their strategy in proactive Security System Lifecycle Management (SLM).
Here are three ways security teams are making physical security visible, reliable, and easier to manage
From architectural intent to field-ready execution
Every security project starts with carefully crafted specifications, design drawings, and hardware schedules created during planning. But once those documents hit the field, intent often gets lost.
An estimated 30% of initial construction data is lost by the time a building is turned over to the owner. For physical security, this means ‘as-built’ drawings are often ‘as-guessed’ drawings, leaving teams to manage critical infrastructure with incomplete maps
Architects and engineers may specify exact models and placement using legacy tools, but by the time the hardware reaches the site, those specs are buried in static PDFs or scattered across emails and outdated CAD files.
Installers are left guessing. Integrators improvise. And what gets installed rarely matches what was approved. This is the spec gap, and it creates expensive rework, delays, and misaligned expectations.
| Phase | The goal | The industry reality |
|---|---|---|
| Design | Precise specs and device models defined in digital platforms | Specs buried in static PDFs and scattered emails |
| Deployment | Installers follow up-to-date plans with clear documentation | Teams rely on outdated or incomplete drawings |
| Handover | Accurate as-builts reflect final device placement and details | Up to 30% of original data is lost by project completion |
Bringing specs to life with digital floor plans
Digital floor plans close that gap by bringing specs to life. Instead of pushing paper, security teams now layer device data directly onto interactive site maps. Specs become visual, accessible, and traceable from kickoff to commissioning. Devices can be reviewed, repositioned, and verified before anyone picks up a drill.
In addition to significant time savings, this process ensures total alignment between the design and the finished build, preventing the translation errors that often lead to costly field surprises
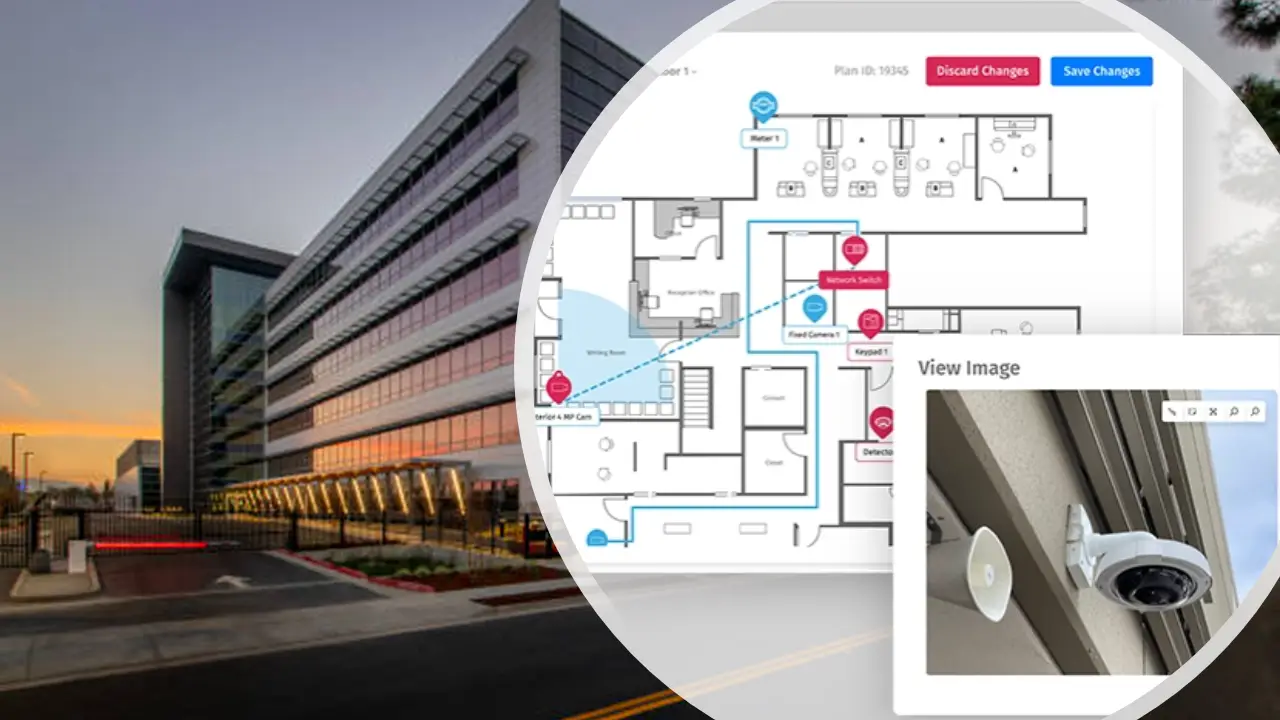
The outcome is a transparent path from design to deployment, where decision-makers operate from a single, real-time source of truth.
Field-level asset intelligence
Once devices are installed, they shouldn’t disappear. But too often, they do.
Walk into almost any large facility and ask a technician what’s behind a specific door or which camera covers a blind spot, and chances are, they’ll need to go hunting.
Field technicians spend up to 35% of their time simply looking for information, hunting for the right junction box, identifying the specific model of a failing reader, or searching for warranty paperwork buried in a binder.
That’s because most physical security teams operate without a single, accurate source of truth. Hardware gets installed, but documentation lags.
The problem goes beyond the hardware. It’s the disconnect between what’s installed and what’s actually documented.
- Device locations exist in people’s heads instead of a shared system.
- Model numbers, firmware versions, and install details are scattered or missing.
- Service history is inconsistent or lost across vendors and tools.
- Warranty status is unclear until after coverage has expired.
Smart devices into smarter decisions
Maintenance logs, if they exist, are buried in spreadsheets or locked away by vendors, creating critical blind spots across both infrastructure and institutional knowledge.
The devices themselves are smarter than ever. Many readers, locks, and cameras are equipped with RFID, NFC, and serial tags that can provide real-time data. But without a way to access that data on the fly, it’s wasted potential.
This is where field-level intelligence changes the game.

With mobile scanning and digital asset records tied to interactive floor plans, technicians no longer have to guess. Scan a tag and instantly see the device’s full history: when it was installed, who serviced it last, warranty status, and even photos of the installation. Issues get identified faster.
Service is smarter. And downtime shrinks. This real-time clarity empowers decision-makers with data they can trust, shifting the organization from a reactive maintenance loop to an operational resilience model.
Building a proactive security lifecycle
Physical security failures rarely happen at a convenient time. A reader goes down during shift change. A compliance audit reveals gaps in device records. Or worse, a system fails, and no one realizes it until after a security event.
Across industries, this may look different, but it always leads to the same outcome: lost time, increased risk, and unplanned costs that could’ve been avoided with better visibility and foresight.
| Visibility gaps across industries | ||
|---|---|---|
| Industry | Common scenario | Operational impact |
| Healthcare | Badge reader fails at a restricted area during a shift | 47% of hospitals report delayed response times due to faulty access controls. |
| Retail | Camera outage in a high-shrink zone goes unnoticed for days | Retail shrink accounted for $112.1B in losses in 2022, much of it preventable with visibility. |
| Manufacturing | Critical door hardware fails on a secured production line | Downtime can cost manufacturers up to $260K per hour, per Aberdeen Group research. |
| Education | Security doors not functioning during emergency drill | 31% of K-12 facilities cite door hardware issues as a barrier to effective emergency response. |
The case for proactive lifecycle management
In many organizations, maintenance still runs on the “fire drill model”: wait for something to break, then scramble to fix it.
But as systems grow more complex and budgets tighten, reactive maintenance becomes too risky. The shift to proactive Security System Lifecycle Management changes that equation.
When every device is tied to a digital record complete with age, service history, and warranty status, teams can spot patterns, predict failures, and plan ahead.
With lifecycle data centralized and visualized, security teams move from gut-feel decision-making to informed, strategic action.
Turning physical security into a strategic asset
Every stage of the security lifecycle matters. When specifications go missing, when installed devices aren’t tracked, and when maintenance relies on guesswork, the result is the same: higher risk, more downtime, and mounting costs.
But the gap between what’s planned and what’s actually in the field is closing and forward-thinking teams are leading the charge.
By adopting digital floor plans, enabling field-level asset intelligence, and shifting from reactive to proactive lifecycle management, security leaders are transforming fragmented systems into unified, strategic infrastructure.
The tools exist, and the teams that embrace them will set the new standard for visibility, reliability, and control.
Want to see how this works in the real world?
Explore how SiteOwl helps security teams take control of the entire lifecycle from design to deployment and beyond!