Table of Contents
- 25 Actionable tips to optimize your physical security program
- How do you ensure that your physical security program is as effective as possible while maintaining a reasonable budget?
- Elements of an effective Physical Security Program
- Site and building design
- Security policies and procedures
- Security Personnel
- Security equipment and technology
- Lifecycle management
- Optimizing your physical security program
25 Actionable tips to optimize your physical security program
Physical security is at the core of every company’s risk management program. A robust physical security program provides a framework to identify risks and measures to address these risks.
Security directors understand the importance of aligning their security program with their organization’s objectives and risk appetite. But here’s the challenge:
How do you ensure that your physical security program is as effective as possible while maintaining a reasonable budget?
The answer is not easy, but it is achievable. While there is no one-size-fits-all solution, there are steps you can take to optimize your program.
At SiteOwl, we take a holistic approach to physical security and believe that the elements that will make a difference to your physical security program are process, people, technology, and data.
In this article, we’ll share 25 actionable tips to optimize your physical security program based on our vast experience helping security directors and integrators digitally transform their physical security programs
Elements of an effective Physical Security Program
The elements of an effective physical security program will vary depending on the type of organization and the risk to which it is exposed. Regardless of the organization, the following five elements are key:
- Site and building design
- Security policies and procedures
- Security personnel
- Security equipment and technology
- Lifecycle management
When all five elements are working well together, organizations can achieve a comprehensive and effective physical security program.
Here are 25 actionable tips to help you optimize your physical security program:
Site and building design
Site and building design features work in concert to detect, delay, and respond to threats. As a security director you must ask yourself what physical security measures are in place at each layer to help reduce risk.
1.Conduct a physical security risk assessment to identify and prioritize risks.
A physical security risk assessment is a systematic process that involves identifying and prioritizing risks that could negatively impact your organization’s operations. You want to perform this assessment at least once per year to identify potential threats and to help you prioritize your security investments.
2.Conduct a Crime Prevention Through Environmental Design (CPTED) assessment.
Crime Prevention Through Environmental Design (CPTED) is a multi-disciplinary approach that uses the physical environment to influence people’s behavior and create an environment to deter crime.
3.Review crime statistics and trends to identify potential threats.
Reviewing crime statistics for your areas of operation can help you identify areas where you should focus your resources and efforts. Crime statistics are also a valuable tool for assessing your security posture.
4.Collaborate with a security specialist or integrator.
Collaborate with a security specialist or integrator to help with your plan and implementation. Security consultants can help you identify and design your organization’s most effective security solution. Integrators can help you determine what hardware and software to purchase and help you with installation, implementation, and ongoing maintenance.
5.Implement physical security controls to mitigate risks.
While it may sound like a no-brainer, many organizations go through the process of performing a risk assessment but fail to implement the necessary physical security controls. In today’s threat landscape, this is not an option.
Security policies and procedures
Security policies and procedures are a set of guidelines that serve as the blueprint for a security program. Security policies and procedures will vary depending on the organization, its risks, and its operational needs. In any security program, there must be a baseline set of policies and procedures.
6.Review current SOPs to ensure they are up to date.
SOPs can be a great asset to your team, but it is important to remember that an SOP is only as good as the information that is included in it.
7.Establish policies and procedures for securing and controlling access to facilities.
Access control policies are central to a robust physical security program and must be documented and communicated to all employees.
8.Liaison with local law enforcement and building management to ensure that your security program is aligned with their policies.
When liaising with local law enforcement and building management, it’s important to consider the bigger picture, especially when aligning with their policies. This requires a multi-faceted approach that considers the specific needs of the facility or property, the legal requirements of the jurisdiction, and the potential risks and threats that might be faced. As security directors, we are responsible for understanding all of these factors and using them to inform our planning and decision-making processes. Ultimately, the goal is to create a security program that is effective and efficient, and well-integrated with the community and the stakeholders it serves.
9.Understand and comply with industry regulations and codes, such as HIPAA, Joint Commission, and OSHA
The importance of security infrastructure cannot be overstated in the modern age. It is essential for organizations to protect both physical and digital assets to maintain stability and trust. However, before installing or upgrading their physical security infrastructure, security directors must first understand and comply with industry regulations and codes such as HIPAA, Joint Commission, and OSHA. These regulations ensure that the security measures meet the necessary standards and prevent any potential liability issues that may arise.
10.Conduct regular security audits to ensure that physical security controls remain effective.
One of the most important steps that security directors can take to ensure the effectiveness of their physical security infrastructure is to conduct regular security audits. These audits can help identify any weaknesses or vulnerabilities in the system and allow for prompt corrective action.
Security Personnel
Security personnel are the people who implement the policies and procedures established in the security program. They include security officers, safety wardens, front desk personnel, facility team members and other staff depending on the type of organization. Regardless of the layout of the facility, it is important that security personnel know how to identify and respond to potential threats.
11.Set a schedule for emergency preparedness training and drills.
By setting a schedule for emergency preparedness training and drills, your physical security team will adopt a proactive approach that will enhance the overall security posture of your organization.
12.Design & maintain an active security awareness program.
An active security awareness program helps enhance overall security awareness and improves security risk management across the enterprise.
13.Build a strong security vendor evaluation and selection framework that aligns with your organization’s needs and objectives.
14.Audit security vendors to ensure compliance.
Once you’ve hired them, you want to ensure that your vendors are in compliance and can support your security standards and policies.
15.Recognize security personnel for outstanding performance.
Physical security teams are not exempt from the human factor that drives a company’s success and, as such, should be recognized for their contributions.
Security equipment and technology
An effective physical security program ensures that physical security equipment and technology, personnel, and processes are properly designed and implemented to protect your organization’s assets. The security director must ask himself, what security technology is in place to help detect, delay, and respond to threats?
16.Conduct a physical security inventory audit to identify and address any gaps
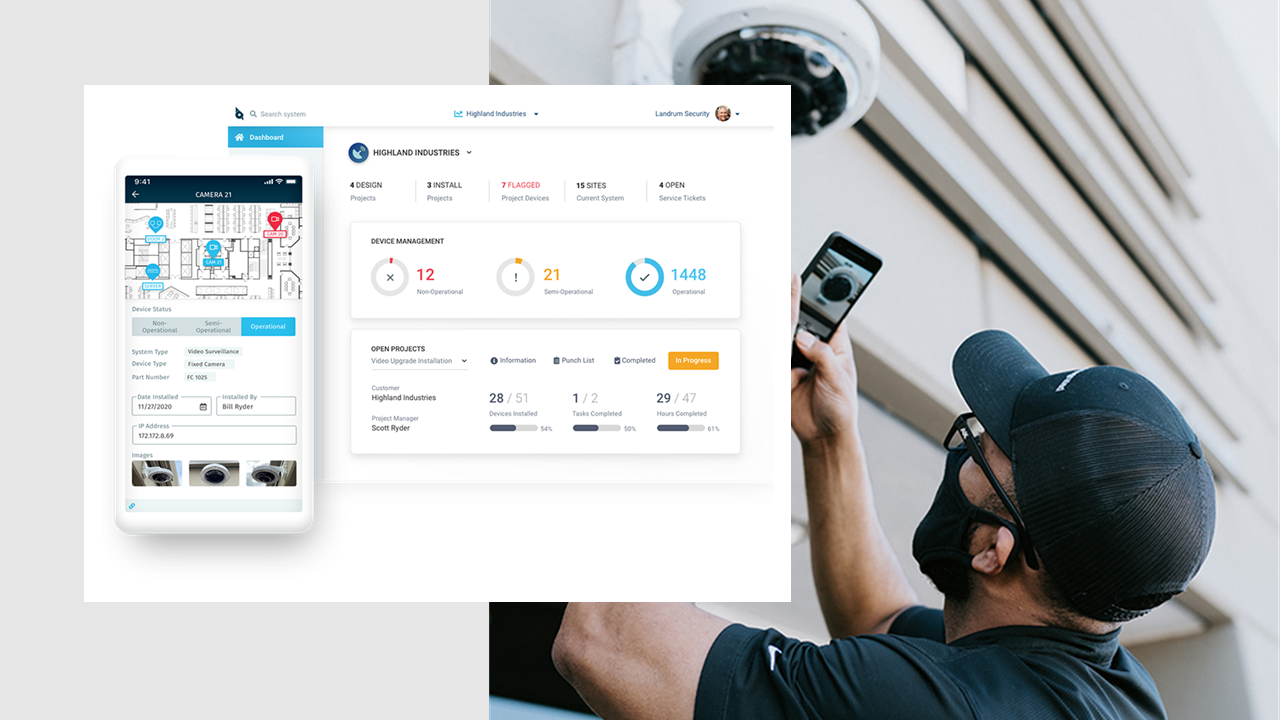
Having an accurate asset inventory ensures your company can keep track of the type and age of hardware in use. In doing so, you gain greater insight into your system’s design and discover ways to improve security without making extensive updates.
17.Identify opportunities for standardization and optimization.
Standardization and optimization are great ways to ensure that your physical security infrastructure is aligned with the organizational goals and objectives.
18.Obtain complete visibility of all your physical security assets.
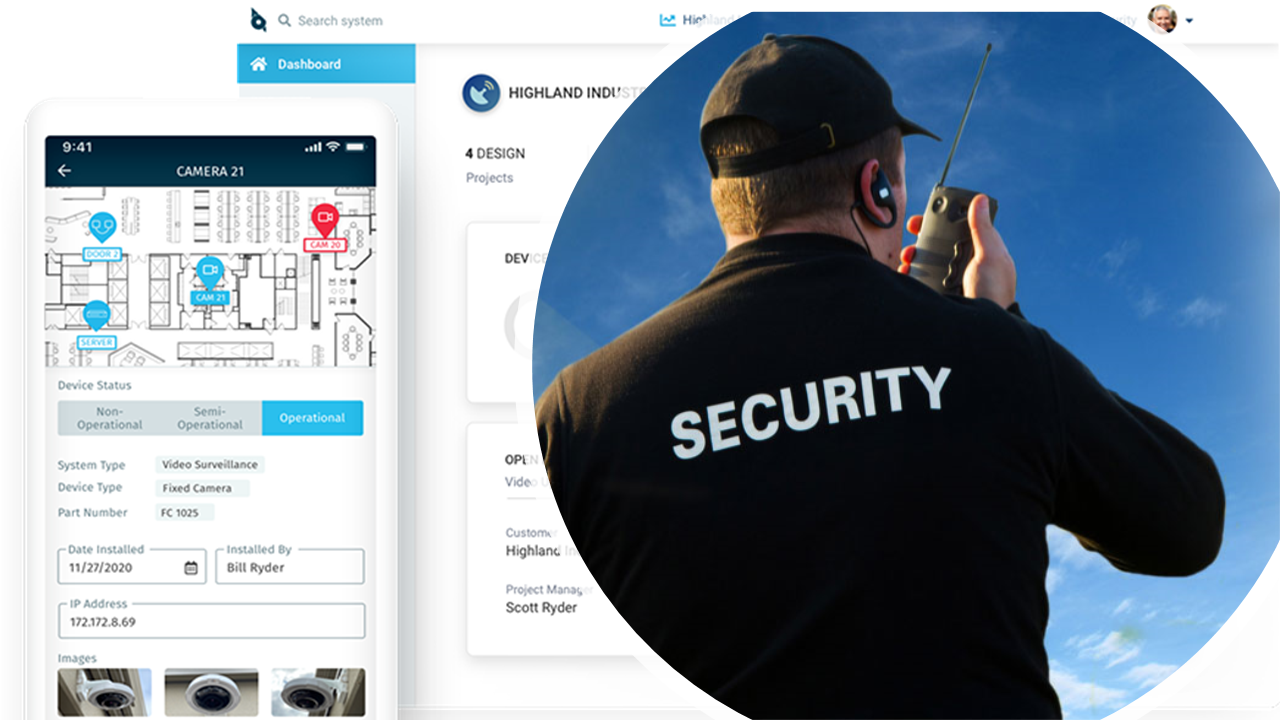
Visibility is critical to managing physical security effectively and efficiently. With visibility, you can manage your physical security effectively. SiteOwl is a physical security management platform that lets you obtain complete visibility of all your physical security assets and capabilities.
19.Establish or review Security Operations Center (SOC) policies.
SOC policies should be in place to ensure that all personnel understand their role and responsibilities and are aware of current and emerging security threats.
20.Equip your team with the tools they need to succeed.
At the end of the day, your physical security program is only as strong as its weakest link and your team needs the right tools to succeed. They need to be able to isolate problems, generate tickets, and address incidents with minimal downtime.
Lifecycle management
Lifecycle management is the process of determining the lifespan of a physical security product or solution and planning the steps to take when it is time to retire the solution and/or its products. But it doesn’t just stop there. Lifecycle management is also about preparing for how to replace or update managed security systems without disrupting or negatively impacting businesses’ day-to-day operations.
21.Establish a centralized record system that improves effectiveness.
By establishing a centralized record system that includes auditing, warranty, and lifecycle management, you will be able to streamline the flow of information and improve the overall performance and reliability of your physical security systems.
22.Put in place vendor compliance with site-specific requirements
Managing vendor relations is an essential part of today’s physical security process. Vendor compliance is a great way to gain a better understanding of the performance of your vendors and partners.
23.Maintain detailed device-level data on all physical security devices
Maintaining detailed device-level data of your physical security devices and resources can be the difference between a safe and secure environment and one that is an incident away from disaster.
24.Institute scalable security system practices.
Scalable security system practices not only strengthen your security posture but also help foster a culture of compliance and improve your security program.
25.Consolidate, track and manage all your system devices.
Physical security lifecycle management comes down to having a solid plan, implementing that plan, and then being able to consolidate, track and manage all your system devices regardless of their location.
Optimize your physical security program
Optimizing your physical security program involves understanding your security needs, knowing how to address them, and how to measure the results of your security investments. In this evolving threat landscape, security directors must constantly reevaluate their programs to meet their organization’s current and future needs.
The elements of a physical security program discussed in this article, along with the actionable tips to optimize your physical security program, can provide you with the information you need to evaluate and ultimately optimize your physical security program. Still, they’re only the tip of the physical security iceberg.
SiteOwl’s mission is to help security directors, integrators, and facility managers improve their physical security programs. Download our physical security lifecycle ebook today for more information on optimizing your physical security program.